Live satellite images & current view of the Earth
Fuel your decision-making with advanced real-time and historical satellite imagery search, intuitive visualizations, and powerful analytical tools — all in one platform:
- Access high-resolution optical (multispectral and stereo) images, SAR data, and terrain maps
- Explore archival and live satellite images from around the globe
- Use 20+ pre-set indices or create custom band combinations
- Tailor workflows to your industry's unique needs

Key features for satellite insights
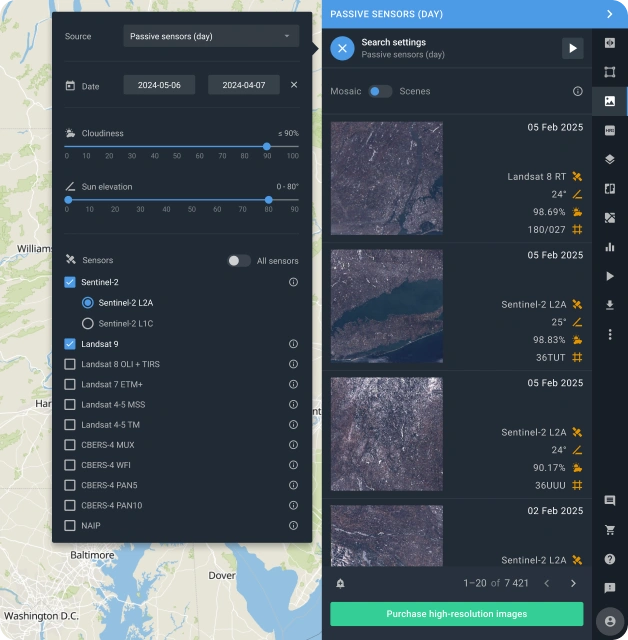
Satellite Imagery Search and Mosaic
Easily find current and historical satellite views based on their capture date and coverage area while filtering out cloudy images. You can view a single satellite image in detail or combine multiple images into a seamless mosaic to see larger areas. Works precisely whether you're studying a small field or a whole region.
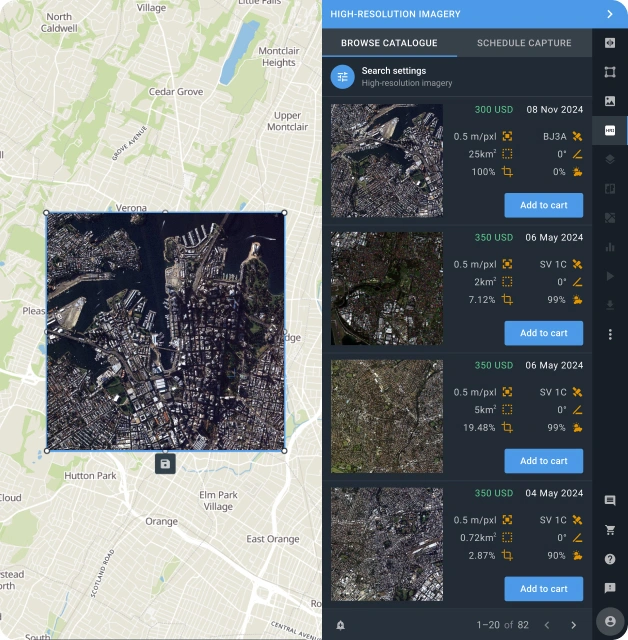
High-Resolution Imagery Archive and Tasking
Get high-resolution imagery (down to 30 cm in detail) from our extensive archive or request the most current satellite images captured specifically for your needs. Use detailed historical and real-time satellite views from leading providers for city planning, infrastructure monitoring, or environmental research.

Customizable Indices and Band Combinations
Choose from over 20 ready-made indices, including NDVI, Color Infrared (Vegetation), and Land/Water, or create custom band combinations to study land features. From current crop health and water distribution to urban density, tailor the analysis to your exact needs.
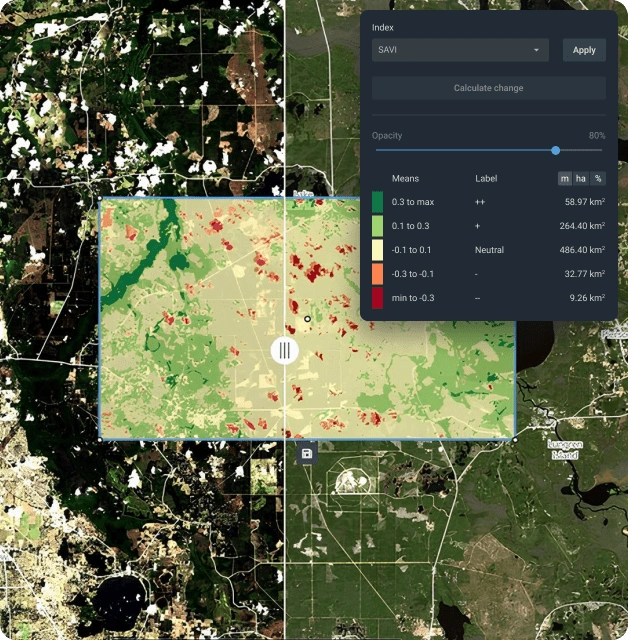
Image Comparison and Change Detection
See exactly what's changed in your areas of interest by comparing current and historical satellite images from different sources. Our automated tools help you spot and measure differences live — whether new buildings, cleared forests, or variations in crop health — with pinpoint accuracy.
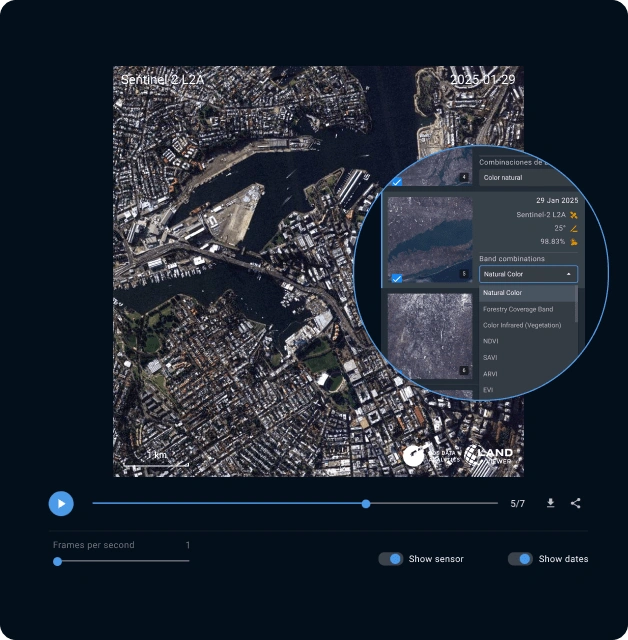
Time-Lapse Animation
Create dynamic visual stories with time-lapse animations based on current and historical satellite imagery. Capture the evolution of landscapes, from city growth and seasonal land use cycles to melting glaciers, and create compelling visuals for presentations and reporting.

Satellite Time Series Analysis
Understand long-term trends using historical satellite images. Choose from multiple indices to monitor seasonal vegetation changes, track urban sprawl, or measure conservation success. See current trends clearly to forecast what’s ahead.
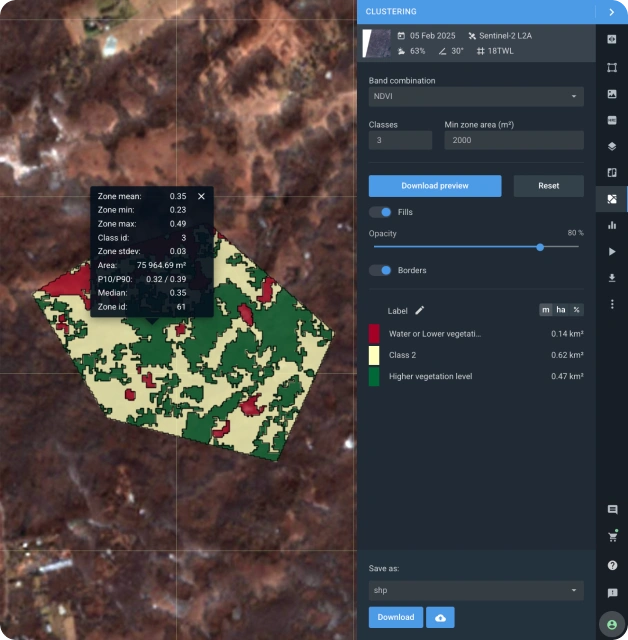
Data Clustering
Turn complex datasets into easy-to-understand groups of satellite data based on spectral similarities. Whether you're monitoring water bodies, tracking crop health, or studying urban areas, this tool automatically finds and groups similar regions, making it simple to understand current patterns and make informed decisions.
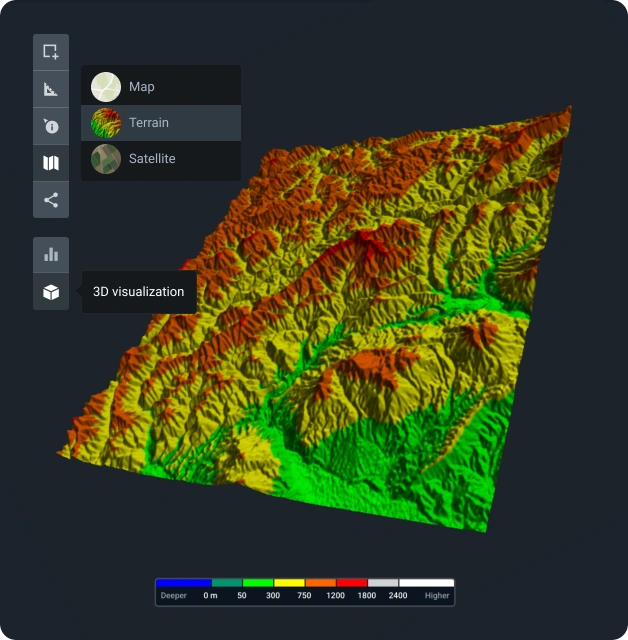
3D Modeling
Transform historical and live satellite imagery into 3D visualizations to better understand terrain and structures. Ideal for planning infrastructure, assessing real-time natural disaster impacts, or conducting geological studies.
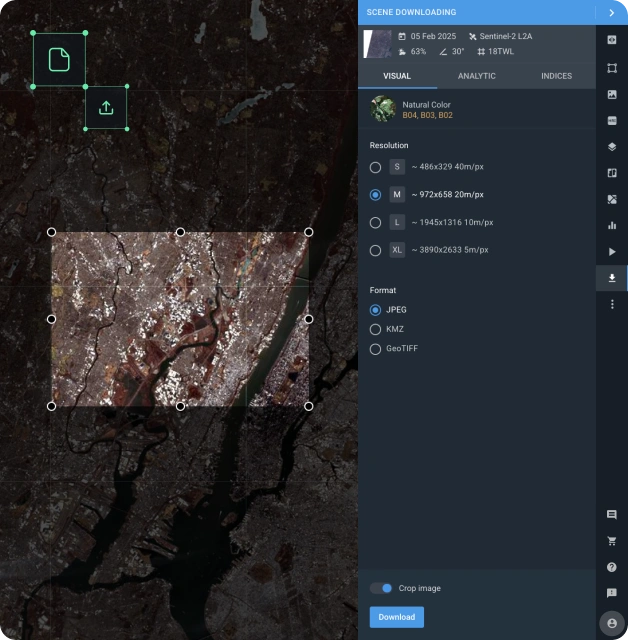
Exporting Imagery and Analytics
Get your live and historical satellite data the way you need it. Download high-quality live imagery and processed analytics or integrate data into GIS tools via WMS (Web Map Service). Share real-time insights with your team or seamlessly include them in larger analytical projects.
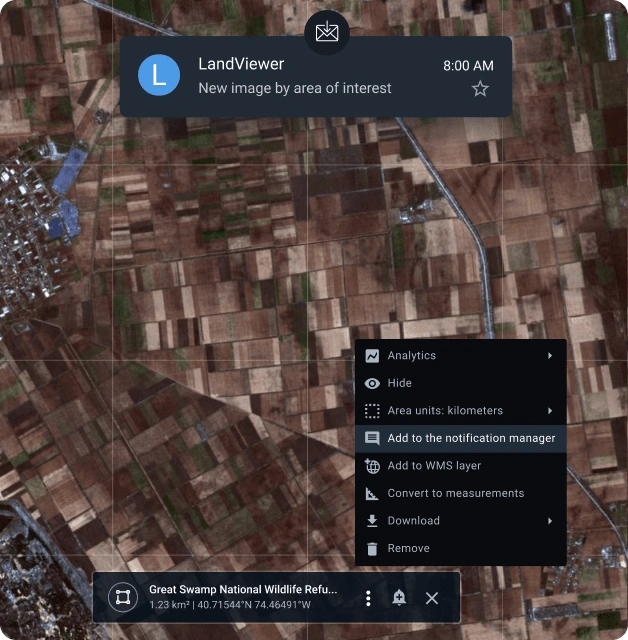
Notifications for Selected Areas
Never miss any live satellite image of your area or a change in key indices. Always stay ahead with real-time alerts tailored to your monitoring needs.
Satellite imagery data providers
Access geospatial data from the world's leading providers:



